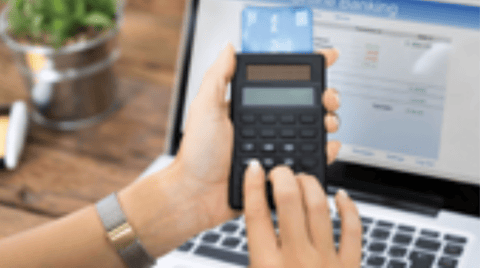
To offer a truly frictionless payment experience, you must unify all your sales channels. Whilst the features in each channel are important, it’s the interactivity between them that makes the real difference.
PXP Financial will help you build an unrivaled commerce experience and best payment journey for your customers based on latest technology.